Leakage Detection And Risk Assessment PHP
Enhancing Security in Online TransactionsIn today’s digital era, online shopping has become an integral part of our lives. With just a few clicks, we can purchase products and services from the comfort of our homes. However, along with the convenience, there is also the concern of data leakage and security breaches. As avid online shoppers, we understand the importance of protecting sensitive information, especially when it comes to debit card details. The existing system falls short in preventing data leakage of debit cards while using online e-commerce websites, leaving users vulnerable to potential attacks.To address this issue, we present our proposed system – Leakage Detection and Risk Assessment using web app. Our team has developed a robust web application that focuses on enhancing security, particularly in the real of payments.Using cutting-edge technologies such as AES Algorithm using PHP, MySQL, HTML, and CSS, our web application provides a safe and secure environment for users to enter their debit card details. One of the key features of our system is the implementation of AES encryption, which ensures that all card details are encrypted, even if there is a breach in data security.Leakage Detection And Risk Assessment: PHP
Leakage Detection And Risk Assessment PHP
Software Requirements: –
Front End: HTML5, CSS3, Bootstrap
Back End: PHP, MYSQL
Control End: Angular Java Script
PHP Tools:
XAMPP 8.1 – 64 bit
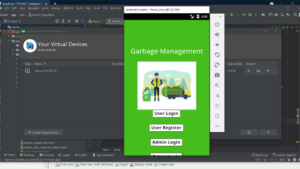
System Modules:
User
- Register and login
- View Products
- Fliter Products
- Buy with Secured Gateway
- Buy with Unsecured Gateway (Using AES)
- Enter Card details
- Place Order
Attacker
View Details
- Secure
- Encrypted with AES
- Card details are encrypted
- Unsecure
- Attack and leak the card details
Module Description:
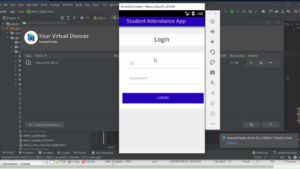
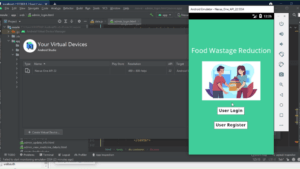
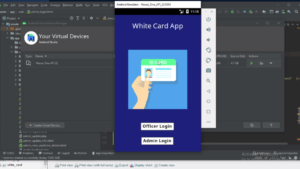
Register Login Module:-
In login module the customer and merchants can login to the application if they already created their account and signed in.
Purchase Items:
User purchase some items through online with their online payment. When we use online payment we have enter our card details also.
View Details:
After user purchasing attacker enter the system and view the user transactions details. Like card number, pin number and etc.
Secured Payment
With our AES algorithm, we ensure that user data is encrypted and protected from potential attackers.
Unsecured Payment
With plain text, data will be leaked to browser cookies, hence the attacker will leak user data.